Authentication - Multi-Factor Auth, Single Sign-on
Day 17 - Error Identification and Suggestions
You're checking out on an e-commerce site. You click Submit, and the page reloads with an error message at the top: "There were errors in your submission." That's it. No indication of which fields have problems. No explanation of what's wrong. You start hunting through the form, checking each field, trying to figure out what went wrong.
This frustrating experience is unfortunately common, especially on e-commerce sites, membership portals, and complex forms. But it's also completely avoidable - and fixing it makes your site accessible and more usable for everyone.
Day 12 - Create a deep redirect in a headless site
One of our clients has a custom surveying application built with a Drupal back end, and a VueJS/headless front end. They use this application to record observations in various buildings and sites that don't meet accessibility requirements.
They give their clients access to the front end. This application organizes observations into particular sites, in particular projects, grouped by the requirement. Each observation can have photos attached, along with notes and recommended solutions.
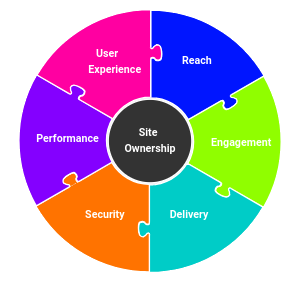
Security
Security is a cornerstone of what we do. All of our ongoing plans include our "Protection Plan" service to keep your site safe, up-to-date, and well backed up. We also provide:
How should I manage my passwords?
May 2014
Heartbleed. The end of XP. Zero-day Internet Explorer attacks. April was a tough month for security on the Internet -- are the days of safe browsing over?
Probably not. But it is time to make sure you have good password management processes -- or learn how to do it if not.
Years ago I wrote about Smarter Password Management, and how to more easily create secure passwords. It's time for a brief update, as the environment has changed a bit.
Confidentiality, Integrity, or Availability
Not 2 weeks after my newsletter calling out how people take for granted that nothing bad will happen to their web sites, two of the biggest providers went down yesterday, Amazon and Akamai, in several separate incide
Hard Passwords made easy
Why use a strong password
In the online world, security plays a role in all online activities. Passwords are the most commonly used method to limit access to specific people. In last month's newsletter, we discussed assessing the relative value of systems protected by passwords, and grouping passwords across locations with similar trustworthiness.
In a nutshell, don't bother creating and remembering strong passwords for low value systems, and certainly don't use the same passwords for low value systems that you use in high value systems.
Smarter Password Management
The problem with weak passwords
Your dog's name. Your anniversary. Your childrens' initials, birthday, or birth weight. Your favorite hobby, or the name of your boat. Which one do you use for your password? Network Administrators and hackers know that most people choose passwords like these to protect anything from logging into web-based bulletin boards to buying things online.
Why does it matter? Identity theft. Corporate espionage. Loss of your data, or digital photos. Do you want to risk these things? In many cases, a weak password is all that separates your data from any bad guy who chooses to impersonate you online, or worse.

